امنیت هدیه ما به شماست
امنیت در دنیای دیجیتال - دیسنا : اولین پایگاه اطلاع رسانی فضای تبادل اطلاعاتامنیت هدیه ما به شماست
امنیت در دنیای دیجیتال - دیسنا : اولین پایگاه اطلاع رسانی فضای تبادل اطلاعاتWebroot Secure Anywhere Version 8.0.1.229 ارائه شد .
شرکت امنیتی وب روت Webroot ، پیشرو در ارائه راهکارهای امنیتی و ضد ویروس ، امروز محصولات آنتی ویروس خانگی و شرکتی خود را بروزرسانی کرد .
این نسخه با نام Version 8.0.1.229 ارائه شده است و به صورت کاملا خودکار بر روی آنتی ویروسهای کاربران وب روت بروزرسانی می شود .
در این نسخه بجزء بهینه سازی برخی ویژگی های نسخه قبلی ، ویژگی های جدیدی نیز افزوده شده است .
برخی ویژگی های بهینه سازی شده :
- Compatibility with:
- Avast
- XChat
- UltraMon
- ConstantGuard ID Vault
- Watchdog
- Synaptics PS2 keyboard drivers
- Multiple performance enhancements, including:
- Reduced CPU load with numerous instances of Chrome
- Reduced background CPU usage during scan
- Uninstall process and performance enhancement
- CPU usage when on the status screen
- Reduced overhead of background threads while idle
- Keyboard responsiveness with Identity Shield
- (Business edition only) Increased server process shutdown speed
- Significant threat detection and remediation enhancements, including:
- CLSID cleanup
- Kernel rootkit removal
- Heuristic blocking of files with appended data
- Context menu scans now support a significantly larger number of files
- Windows 8 kernel support
- Change journal support on 64-bit OS's
- Exception tracking logic
- Web Threat Shield blocking behavior
- Updating from a previous version
- Updated install and update process to prevent invalid paths
- Reliability of status screen updates
برخی ویژگی هایی که به تازگی افزوده شده است :
- New language support for:
- Traditional Chinese
- System Cleaner cleanup for Chrome
- Scheduling for System Cleaner
- System cleanup of Office 2003, 2007 and 2010 most recently used files list
- New threat detections:
- M0rpheus
- Zeus Trojan
- General malicious services
- Enhanced zero-day threat prevention and warnings
- Cleanup of .exe subkeys
- Additional logging of active processes
- Help and Support link in tray options
- Desktop shortcut after install
- (Business edition only) Logging when agent command scans are run
برخی نقصهای برطرف شده :
- Simultaneous initial scans
- Caps Lock unexpected behavior on secure sites
- Last scan display discrepancies
- Context menu scans failure
- Scheduled scan on boot up
- (Business edition only) Handling of Account Management Website activation
- Correct completion of active scans
- Duplicate uninstall links
- Identifying host file modifications
- Scanning of some corrupt files
- Duplicate prompts for untrusted program execution
- Premature scan completion
- Not scanning on battery power
دیگر تغییرات :
- Major UI enhancements
- Changed international product names to prevent language confusion
- Help question mark in upper-right corner of UI now opens support web page
- (Business edition only) User response option removed for firewall prompts in centrally managed environment
اخبار مرتبط :
همکاری شرکتهای Webroot و Corero Network Security
بررسی آنتی ویروس Webroot توسط ITPRO
Webroot سبکترین آنتی ویروس در AV-TEST
شبکه هوشمند وب روت ( Webroot® Intelligence Network )
همکاری استراتژیک F5 Network و Webroot
Webroot Release Notes - Version 8.0.1.193
W32.Flamer اولین بار توسط Webroot شناسایی شده است .
Webroot برنده جایزه ادیسون 2012
همکاری InsightCloud و Webroot برای توسعه کسب و کار امنیت Endpoint

تهدیدات SIREFEF/ZACCESS با تکنیکهای جدید آمدند .

دیسنا - پایگاه اطلاع رسانی امنیت اطلاعات ایران .
شرکت امنیتی ترندمیکرو - پیشرو در ارائه راهکارهای امنیتی تهدیداتی را شناسایی کرده است که نسخه های قبلی آنها پیش از این مورد شناسایی قرار گرفته اند ولی اینبار با تکنیکهای جدیدی آمده اند تا کاربران را هدف حملات خود قرار دهند .
During the last weeks of July, we received reports from customers that their services.exe files were being patched by an unknown malware. The patched services.exe, detected by Trend Micro as PTCH_ZACCESS (for 32-bit version) and PTCH64_ZACCESS (for 64-bit version), was verified to be a component of the SIREFEF/ZACCESS malware family. ZACCESS (also known as ZEROACCESS) used this patched system file to run its other malicious components upon reboot. This proved to be a new variant of SIREFEF/ZACCESS, which now uses user-mode technique to stealthily load its malicious code, instead of using regular rootkit techniques.
Investigating these cases further using the Trend Micro™ Smart Protection Network™, we were able to locate the main malware (BKDR_ZACCESS.SMQQ) responsible for patching services.exe. We also identified all of the components related to its infection routine. We found that the infection started with the execution of K-Lite Codec Pack.exe (downloaded by the user) and resulted to the patching and executing of the patched services.exe.

This malware propagates by bundling the main malware in crack/keygen applications or game installers. It can also disguise itself as a required codec that needs to be installed to play a downloaded movie via peer-to-peer (P2P) applications, which can be found on sites dedicated to keygen apps or in P2P services. Below are some of the names used. Note that these file names contain popular movies:
Downloaded binary via P2P:
- %P2P DL folder%\The_Hunger_Games_2012_DVDRip_XviD_AMV\K-Lite Codec Pack 9.0.exe
- %P2P DL folder%\Alien_1979_DVDRip_XviD_FKG\K-Lite Codec Pack 9.0.exe
- %P2P DL folder%\The_Amazing_Spider-Man_2012_DVDRip_XviD_YKG\K-Lite Codec Pack 9.0.exe
- %P2P DL folder%\John_Carter_2012_DVDRip_XviD_IIN\K-Lite Codec Pack 9.0.exe
- %P2P DL folder%\The_Dark_Knight_Rises_2012_DVDRip_XviD_QEV\K-Lite Codec Pack 9.0.exe
%P2P DL folder%\ refers to the P2P folder where the file is being saved after downloading it.
Downloaded binary via direct download:
- Diablo_III_crack.exe
- Microsoft_Office_Professional.crack.exe
- Youtube_Grabber_Keygen.exe
Binary Planting Technique
Once installed, the main ZACCESS dropper (detected as BKDR_ZACCESS.KP) checks the current user privileges. If the user is an administrator, the malware continues its installation routine. But if the user is a non-administrator user, the malware elevates its privileges to proceed with malware installation. The malware drops and executes BKDR_ZACCESS.SMQQ, which causes a User Account Control (UAC) notification to appear onscreen.
When it appears, users may possibly not allow the file to execute, thinking that the file is suspicious, halting the ZACCESS installation. To bypass this, ZACCESS forces the UAC dialog box to pop up by executing a non-malicious Adobe Flash installer (InstallerFlashPlayer.exe).
To do this, ZACCESS drops InstallerFlashPlayer.exe and the malicious file msimg32.dll (BKDR_ZACCESS.SMQQ) in the user temporary folder. This technique is known as binary planting, a form of DLL Search Order abuse, that ensures the loading of the ZACCESS malicious code into the InstallerFlashPlayer process address when it is executed. By default, when InstallerFlashPlayer.exe is executed, Windows looks for the msimg32.dll in the current folder before searching the Windows system folder. Because BKDR_ZACCESS.KP dropped the malicious msimg32.dll into the current directory, Windows loads the malicious code instead of the original one.


Infection Worldwide
Our research noted a sudden increase in ZACCESS/SIREFEF infections in July 2012. Based on the data we gathered from the Smart Protection Network™, below is a chart representing the number of affected machines by this new ZACCESS variant:

Among countries affected, the United States had the most number of infections compared to other countries such as Japan, Australia and the United Kingdom.

دیسنا :
پایگاه اطلاع رسانی امنیت فناوری اطلاعات ایران

توضیحات ترندمیکرو درباره ویروس Shamoon - WORM_DISTTRACK.A

دیسنا - پایگاه اطلاع رسانی امنیت اطلاعات ایران .
شرکت امنیتی ترندمیکرو در وبلاگ خود توضیحاتی را درباره ویروس ( حمله سایبری ) Shampoon که با نامهای Disttrack/Shamoon ، WORM_DISTTRACK شناسایی می شود داده است .
قطعات این ویروس نیز با نامهای دیگری مانند TROJ_WIPMBR.A و TROJ_DISTTRACK.A
، توسط محصولات ضد ویروس ترندمیکرو می شوند و کاربران دربرابر این ویروس مورد
حفاظت قرار می گیرند.
اطلاعات بیشتر در لینکهای زیر موجود است و ترندمیکرو اطلاعات تکمیلی را بر روی همین لینک به روز رسانی می کند .
دیسنا :
پایگاه اطلاع رسانی امنیت فناوری اطلاعات ایران

مدیریت پسوردها : DirectPass: Password management


مدیریت پسوردها همواره یکی از دغدغه های کاربران اینترنت بوده است .
![]()
پسوردها کلیدهای عبور ما برای دسترسی به ایمیلها ، وب سایتها ، فرومها ، وبلاگها و دیگر مکانهایی که ما در آنها حضور داریم.
با برنامه زیر برای مدت نا محدود و با امنیت کامل از کامپیوتر و موبایل ( اندروید و اپل ) می توانید پسوردهای خود را مدیریت کنید .![]()
دیسنا :
پایگاه اطلاع رسانی امنیت فناوری اطلاعات ایران

About Webroot SecureAnywhere Endpoint Protection
خبرهای Webroot در دیسنا

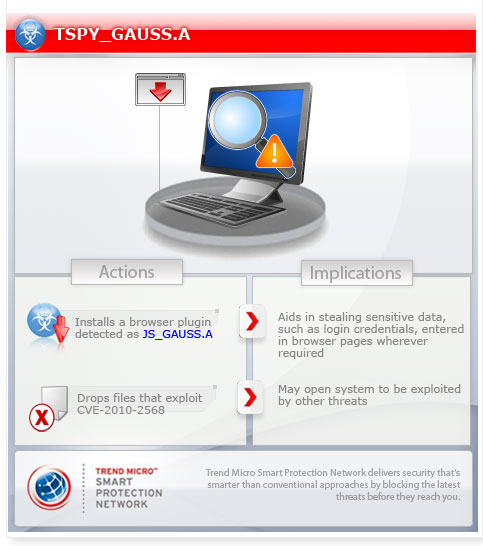
توضیحات ترندمیکرو درباره ویروس گاوس ( Gauss )

دیسنا - پایگاه اطلاع رسانی امنیت اطلاعات ایران .
همانطور که می دانید چندی پیش ویروس جدیدی با نام گاوس شناسایی شده است که اقدام به سرقت اطلاعات محرمانه مخصوصآ اطلاعات مالی و بانکی می کند .
شرکت امنیتی ترندمیکرو پیشرو در ارائه راهکارهای امنیتی و آنتی ویروس در
این زمینه مطالبی را بر روی وبلاگ خود قرار داده است که مشاهده آن خالی از
لطف نیست .


دیسنا :
پایگاه اطلاع رسانی امنیت فناوری اطلاعات ایران

افزودن قابلیتهای جدید به Smart Protection Network


دیسنا - پایگاه اطلاع رسانی امنیت اطلاعات ایران .

CUPERTINO, Calif., Aug. 7, 2012 /PRNewswire/ -- Trend Micro Inc. (TYO: 4704;TSE: 4704), the global leader in cloud security, today announced an expansion of the Trend Micro™ Smart Protection Network™, the cloud-based security infrastructure introduced in 2008 that powers most of the company's products and services. The latest iteration of the Smart Protection Network incorporates advanced big data analytic capabilities that enable Trend Micro to identify new security threats across a broader range of data sources, delivering global threat intelligence that stops threats even faster than before.
These capabilities, especially crucial in the era of mobility, cloud adoption, and advanced persistent threats and targeted attacks, have been integrated into the Smart Protection Network in order to tackle the dramatic volume, variety, and velocity of threats. With this announcement, the Smart Protection Network now includes:
- Newly added technologies, including mobile app reputation (for mobile threats), vulnerability rules (for vulnerability and exploits), network inspection rules (for network communications), and in-the-cloud whitelisting (for minimizing false positives). These combine with the Smart Protection Network's existing reputation technologies -- Web reputation, Email reputation, and File reputation – to further Trend Micro's global threat intelligence, one of the most comprehensive in the world.
- New, custom tools to correlate critical relationships among all the components of an attack, and model cybercriminal behavior and the environments they work in to quickly determine whether something is good or bad. This modeling allows Trend Micro to proactively identify new threats from the data streams using behavioral-based identification methods. By correlating global threat intelligence across many threat vectors, Trend Micro delivers protection against the wide variety of attacks today.
- An evolved cloud infrastructure, allowing for a greater capacity to collect massive amounts of threat data without consuming bandwidth on customers' networks and endpoints. Trend Micro was one of the first security companies to move beyond the conventional approach of resident protection and utilize the power of the cloud to block threats before they reach users. The Smart Protection Network provides automated protection through its cloud infrastructure enabling Trend Micro to protect customers across physical, mobile, virtual, and cloud environments.
Trend Micro customers benefit from these new capabilities, receiving real-time protection against today's threats through efficient and easy-to-manage security products such as Trend Micro Deep Security – the company's flagship product for physical, virtual and cloud environments; Trend Micro Deep Discovery – an innovative Advanced Persistent Threat detection solution; and Trend Micro Titanium for consumer endpoint security.
The Threat Landscape: Then and Now
Today's threat environment means vendors have to deal with the 3Vs of threats: volume, variety, and velocity. Each of these is growing at an astounding rate and has required a shift in how security vendors manage today's threats, especially as cloud adoption, personal mobile device usage, and targeted cyber attacks increase. In 2008, Trend Micro identified one million malware samples, compared to 30 million unique threats Trend Micro is currently tracking for 2012. Mobile threats are also on the rise: In 2008, Trend Micro detected less than 100 threats designed for mobile devices; by comparison, in 2012, Trend Micro has already identified almost 27,000 new malicious apps for the Android platform alone.
Within this new threat environment, the amount of data is also on the rise and constantly on the move -- from cloud to servers to endpoints to mobile devices. According to IDC, the amount of data needing protection will grow by a factor of 90 by 2020. To address these trends, the Trend Micro Smart Protection Network enables organizations and individuals to take a more data-centric approach to security. Unlike traditional, perimeter-centric security, which assumed protectable boundaries surround critical data, the Smart Protection Network protects data wherever it resides.
The Smart Protection Network: Then and Now
With the introduction of the Smart Protection Network in 2008, Trend Micro marked a new approach to security where less reliance was placed on time-consuming pattern-downloads on the client, and more emphasis was placed on stopping threats at their source – in the cloud. Trend Micro was one of the first security vendors to use cloud-based technology to block threats before they reach a network or endpoint.
Since 2008, Trend Micro has continued to evolve and adapt the Smart Protection Network according to the changing threat landscape, and the way businesses and consumers use technology. The proof is in the numbers: In the beginning, the Smart Protection Network managed 5 billion URL, email, and file queries per day. By 2012, that number has more than tripled to 16+ billion queries per day. Likewise, in 2008, the Smart Protection Network analyzed 1 terabyte of threat data daily, compared to the more than 6 terabytes of data it analyzes now.
Today, the Smart Protection Network identifies and blocks over 200 million threats a day – that's over 2300 threats per second. The cloud-based infrastructure, which identifies, correlates, and analyzes new threats, is backed by research labs in 12 regions around the globe, and 1200 security experts worldwide working on surveillance and prevention.
Supporting quotes
Dan Schiappa, senior vice president, identity and data protection, RSA, The Security Division of EMC"The ability to combat cybercriminals requires a far more purposeful collaboration within the industry – such as that between RSA and Trend Micro – and a strong security ecosystem focused on sharing actionable information and mitigating risk. Our RSA® FraudAction service which is designed to help give our customers early warning about a broad variety of cyber threats, leverages real-time global threat intelligence data about viruses, spyware, spam and other malware from the Trend Micro Smart Protection Network. Trend Micro's move to enhance and expand the Smart Protection Network will benefit our customers who rely on multiple sources of threat intelligence data to better understand and fight against multi-vector cyber threats."
Eva Chen, CEO, Trend Micro"Since the launch of the Smart Protection Network in 2008, the threat landscape has shifted to now focus on mobility and targeted attacks. Threats and cybercriminal attacks have taken on an unprecedented level of volume, variety, and velocity. These changes demand a smarter, accelerated approach to security so that our customers can confidently embrace the mobile device and cloud-era, knowing their data is protected, no matter where it resides."
AvailabilityThe next-generation Trend Micro Smart Protection Network is strategically integrated into all of Trend Micro products and services including mobile, endpoint, server, network, messaging, gateway, and SaaS offerings for consumers and businesses of all sizes. Today, 48 of the top 50 global corporations rely on Trend Micro's ability to collect, identify and protect through the Smart Protection Network and ensure the volume, velocity and variety of threat data is managed efficiently and effectively.
For those organizations that have limited bandwidth or are concerned with privacy, Trend Micro offers the Smart Protection Server, ensuring communications and queries stay within the local network.
New Trend Micro Threat Intelligence Services are also now available to very large enterprises, government organizations and other partners. These services enable organizations to use actionable intelligence from the Trend Micro Smart Protection Network to build or enhance their security infrastructure for counteracting data breaches and other potential threats.
The Smart Protection Network also powers Trend Micro's free online tools:
- Trend Micro™ HouseCall™, an on-demand antivirus software scanner for identifying and removing viruses, trojans, worms, unwanted browser plugins, and other malware software.
- Trend Micro™ HouseCall™ for Mobile, which scans Android devices for infected, Trojanized and malicious apps.
- Trend Micro™ Smart Surfing for iPhone, iPad and iPod Touch devices, which provides a smarter, safer experience when surfing the web from an Apple device.
- Trend Micro™ ThreatWatch app for iPhone and Android aggregates and delivers threat intelligence news to a mobile device, giving security professionals, organizations and individuals an easy way to stay up to date on the latest threats right from their mobile devices.
Supporting materials:
For more information about these products, contact your Trend Micro representative or channel partner or visit: http://www.smartprotectionnetwork.com.
For more information about the Smart Protection Network, please visit the new landing page.
About Trend MicroTrend Micro Incorporated (TYO: 4704;TSE: 4704), the global cloud security, creates a world safe for exchanging digital information with its Internet content security and threat management solutions for businesses and consumers. A pioneer in server security with over 20 years' experience, we deliver top-ranked client, server and cloud-based security that fits our customers' and partners' needs, stops new threats faster, and protects data in physical, virtualized and cloud environments. Powered by the industry-leading Trend Micro Smart Protection Network cloud computing security infrastructure, our products and services stop threats where they emerge – from the Internet. They are supported by 1,000+ threat intelligence experts around the globe.
دیسنا :
پایگاه اطلاع رسانی امنیت فناوری اطلاعات ایران
تغییر قیمتها و شرایط لایسنسها ، سرقت فنی ادبی و بررسی اوضاع در



باید گفت این ویروس پیش از این توسط ترندمیکرو شناسایی شده و از شانس بد کسپرسکی این ویروس جزء آن دسته از ویروسها نیست که فقط شناسایی شده باشد و درباره آن مطلبی وجود نداشته باشد ( مانند ویروس فلیم یا شعله ) ، بلکه خبر آن حدود 6 ماه پیش در سایت ترندمیکرو منتشر شده است .
این اولین بار نیست که کسپرسکی با سرقت نام ویروسها و یا اجزای ویروسهایی
که پیش از این کشف شده اند گاهآ با نامگذاری های جدیدی بر روی ویروسهای قدیمی ،
اقدام به خبرسازی برای تبلیغات می کند .
پیش از این کسپرسکی ویروس فلیم ( شعله ) را از شرکت وب روت و ویروس مهدی را
از شرکتهای سوفوس و مکآفی سرقت و درباره آنها خبر منتشر کرده بود و طوری
وانمود کرده که ظاهرآ خود این تهدیدات را کشف کرده است .
البته شاید کسپرسکی تازه این تهدیدات را به تازگی کشف کرده باشد و این طبیعیست .
تعداد
متخصصین و شبکه های تحلیل و پردازش تهدیدات کسپرسکی بسیار کوچکتر از
کمپانی های بزرگ و معتبر بین المللی است و انتظار بیشتری هم از این شرکت
نمی رود .
کمپانی های بزرگ و معتبر بین المللی روزانه تا 100 هزار قطعه
ویروس ، بدافزار و حملات سایبری جدید کشف و شناسایی می کنند و طبیعیست که امکان
انتشار خبر درباره تک تک
این تهدیدات برای آنها امکانپذیر نیست و فقط الگوریتمهای شناسایی
این تهدیدات را بر روی سرویسها و نرم افزارهای خود قرار می دهند تا
کاربرانشان در امنیت باشند .
بخشی از این تهدیدات نیز به وسیله
تکنولوژی های منحصر بفرد امنیتی این شرکتها مانند رفتار شناسی ، امنیت ابری
و یا دیگر تکنولوژی ها شناسایی می شوند و هیچگاه خبری درباره آنها منتشر
نشده و یا تحلیل نمی شوند .
بسیاری از ویروسهایی که این شرکتها کشف و شناسایی می کنند جزء سارقان هویت و
یا جاسوس افزارها و بسیار خطرناک بوده ، ولی کشف و رهگیری اینگونه
ویروسها برای متخصصین حرفه ای این شرکتها به امری عادی و طبیعی تبدیل شده
است .
کسپرسکی با ترفند جدیدی برخی از همین ویروسها که ماهها یا سالها بعد به
دست می آورد را تحلیل کرده و خبر آنها را به نام خود منتشر می کند .
کسپرسکی به واسطه از دست دادن نمایندگان ، مدیران منطقه ای و مشتریانش در
وضع خوبی به سر نمی برد و الارقم اینکه ارتباط خود با دولت روسیه را رد می کند ولی
مشخص است هم اکنون بدون کمکهای دولت روسیه قادر به ادامه حیات نیست .
این شرکت چندین بار نیز سابقه مسدود کردن اشتباهی لایسنسهایش را دارد که
همچین اتفاقی تاکنون در دیگر شرکتهای امنیتی و نرم افزاری سابقه نداشته و این موضوع نشان دهنده نهایت بی مسئولیتی این شرکت است .
خبر منتشر شده توسط کسپرسکی ( 8 آگوست 2012 )
خبر منتشر شده توسط ترندمیکرو 4 مارچ 2012 ( حدود 5 ماه پیش )
خوب به موضوع جدیدی بپردازیم و آن بررسی بازار آنتی ویروس هندوستان است .
همانطور که مشاهده می کنید حدود 1 سالی است که تمرکز تبلیغاتی کسپرسکی به منطقه ایران و خاورمیانه محدود شده است .
شواهد بسیاری نشان می دهد که نه تنها بازار اروپا ، آمریکا و آسیای جنوب شرقی جایگاهی برای این شرکت روس قائل نشده اند ، بلکه بازار آنتی ویروس هند هم که روزگاری به لطف فعالیتهای توزیع کننده انحصاری کسپرسکی در هند Zoom Technology و البته قیمتهای بسیار پایین توانسته بود اندک جایی برایش باز کند ، به سرعت در حال از دست دادن جایگاه خود و خروج از بازار بزرگ هندوستان است .
( Zoom Technology بین سالهای 2009/2010 با کسپرسکی قطع ارتباط کرد و کسپرسکی برای مدتی دست به دامن کامگارد شد . )
کسپرسکی دست به دامن کامگارد شد .
کسپرسکی مجبور به حذف کامگارد شد .
در هندوستان کسپرسکی نه تنها مجبور شده تا قیمت پایه محصولات خود مخصوصآ آنتی ویروسهای تحت شبکه را مجددآ کاهش دهد ، بلکه تخفیفهای جدیدی را نیز به خریداران پیشنهاد داده است .
برای مثال قیمت پایه ( Base ) لایسنس KBSS برای 10 تا 15 کامپیوتر که حدود 1700 روپیه بود ، هم اکنون به 1200 روپیه رسیده است .
البته در زمان قیمت 1700 روپیه قیمت هر روپیه 20 تومان بود و با توجه به اینکه تغییر قیمتی بین دلار و رویپه شاهد نبودیم ، 1200 روپیه می شود 30 هزار تومان می شود .
بد نیست بدانید کسپرسکی همان نسخه KBSS را با عنوان KBSS Small Office به صورت نیم بها ارائه می دهد . این راهکارها با نسخه های Small Business ایران متفاوت بوده و همان لایسنس KBSS تحویل خریدار می شود .
این کاهش قیمت در تعدادهای بیشتر و یا راهکارهای دیگر بیشتر هم می شود .
همچنین میزان تخفیف مهاجرت و تمدید از 30% قیمت پایه به بیش از 60% افزایش یافته است .
جالب اینکه در این مدت قیمت محصولات شرکتهای بین المللی مانند ترندمیکرو و سایمنتک یا تغییری نداشته و در برخی محصولات با افزایش هم روبرو بوده است .
کمپانی های معتبر امنیتی که همواره در همه بازارها جزء انتخابهای اول مصرف کنندگان هستند به دلیل کیفیت بالا محصول و خدمات پشتیبانی و درخواستهای رو به رشد و قابل اعتماد بودن اندکی هم با افزایش قیمت مواجه بوده اند .
ولی در این سالها بجزء شرکتهای امنیتی بین المللی و معتبر ، مشکل دیگری هم برای این شرکت روسی به وجود آمده که آنطور که مشخص است امید بازگشت کسپرسکی به بازار این منطقه را به شدت کاهش داده است .
بعد از بروز مشکلاتی که در جریان هستید مصرف کنندگان محصولات این شرکت به 2 گروه تقسیم شده اند .
گروهی به سمت استفاده از محصولات شرکتهای بزرگ و معتبر امنیتی رفته اند .
و گروه دیگر که محصولاتی با قیمتهای پایینتر و وطنی ( هندی ) می خواهند به سمت استفاده از محصولات ضد ویروس هندی متمایل شده اند .
آنطور که در لابلای برخی وب سایتهای تحلیل و بررسی محصولات و بازار ضد ویروس هند مشخص است ، مصرف کنندگان قدیمی کسپرسکی که هم اکنون از ضد ویروسهای هندی استفاده می کنند معتقدند که علاوه بر پشتیبانی بهتر ، محصولات این شرکتها کیفیت و عملکرد بهتری نسبت به کسپرسکی داشته و این موضوع روند مهاجرت از کسپرسکی به ضد ویروسهای هندی را تسریع بخشیده و دقیقآ همین موضوع مشکلات بسیاری را برای کسپرسکی ایجاد کرده است.
در حال حاضر هند دارای 4 تولید کننده آنتی ویروس است . ( کوئیک هیل ، K7 ، ای اسکن و نت پروتکتور )
این مشکلات به حدی است که کسپرسکی دیگر تمرکزی بر روی بازار منطقه هندوستان نداشته و با ناامیدی با کاهش قیمتها سعی در جذب مجدد بازار دارد و تمرکز تبلیغاتی خود را به ایران و خاورمیانه معطوف کرده است .
- ترس کسپرسکی از افشای قیمتهای واقعی محصولاتش .
بد نیست درباره قیمتهای سال 2012 کسپرسکی اطلاعات بیشتری داشته باشید .
از اوایل سال 2012 کسپرسکی فقط به چند توزیع کننده خاص لیست قیمتهای 2012 را ارائه داده و تاکید کرده که لیست نباید به هیچ همکار و نماینده ای داده شود و نمایندگان از لیست قیمتهای قدیمی استفاده می کنند و در بیشتر موارد قیمت به صورت پروژه ای به نماینده اعلام می شود .
- همکاری شاتل با کسپرسکی .
بد نیست بدانید کسپرسکی از سر ناچاری هر شرایطی که شاتل خواسته برآورده کرده و حتی بیش از 1 سال نام این شرکت را در لیست نمایندگانش قرار داد تا شاید راضی شود با این شرکت همکاری کند .
- تغییرات در سیستم مدیریت لایسنسهای آنتی ویروس کسپرسکی .
همانطور که می دانید کسپرسکی تغییراتی در سیستم مدیریت لایسنسهای خود داده که به واسطه آن در تعداد نصبهای لایسنسهای کسپرسکی محدودیتهایی بروز کرده است . لینک
مثلا در لایسنس 1 کامپیوتره ، کاربر فقط 2-3 بار قادر به تعویض ویندوز و یا انتقال به سیستم دیگر و یا تغییرات سخت افزاری است و سپس لایسنس مسدود ( بلاک ) می شود .
خوب به نظر شما چرا کسپرسکی سیستم لایسنس محصولات خود را به این شکل درآورده است ؟
برخی معتقدند که این تغییرات برای امنیت بیشتر لایسنس است .
ولی باید گفت این استدلال بی ربطی است .
زیرا کاربر دارد روی یک سیستم یا همان تعداد مشخص سیستم از لایسنس استفاده می کند و قوانین Term and Conditions را نقض نکرده که لایسنش مسدود و بلاک شود !
از طرفی می دانید که چندین بار کسپرسکی لایسنسهاش را به اشتباه مسدود کرده است .
ولی یکبار بین سالهای 2009 / 2010 تعداد لایسنسهای مسدود شده هم بسیار زیاد بود و هم متعلق به همه مناطق بود .
یعنی هم لایسنسهای خاورمیانه ، هم هندوستان ، هم انگلستان ، هم منطقه اروپا و هم مالزی و هم آمریکا مسدود شد .
حال با این اطلاعات مشخص می شود که چرا کسپرسکی سیستم لایسنسهای خود را عوض کرده است .
آیا می توانید حدس بزنید ؟
به طور مشخص یکی از دلایل تغییرات در سیستم مدیریت لایسنس ، کسپرسکی سعی دارد که اگر مجددآ بر اثر اشتباه لایسنسهایش مسدود شد به سادگی بر اشتباه خود سرپوش گذاشته و ماست مالی کند و موضوع رو جمع کند و از شواهد مشخص است که دیر یا زود این اتفاق خواهد افتاد .
شرکت شاتل هم که جدیدآ با ترس و لرز فراوان فروش کسپرسکی را آغاز کرده در بخشی از سایت شرایط استفاده از محصولات کسپرسکی رو منتشر کرده که بد نیست مطالعه کنید .
مخصوصآ بند 3.6 که مفهوم آن این است که هر زمان هر محصول و لایسنسی دچار مشکل شد حتی از طرف شرکت تولید کننده و یا خود شاتل ، مصرف کننده حق هیچگونه اعتراضی رو ندارند .
چگونه شاتل فروشنده کسپرسکی شد ؟ ( قسمت اول )
و در آخر باید گفت : متاسفانه برخی خوانندگان وب سایت دیسنا بدون دقت لازم و کافی مطالب دیسنا را مطالعه کرده و به مستندات و منابع دیسنا دقت ندارند .
این گروه از خوانندگان لطفآ در صورتی که با شبهه ای مواجه شدند در ابتدا به منابع و شواهد مندرج در متن و یا ذیل اخبار مراجعه کرده و در صورتی که باز سوالی داشتند آن را با ما مطرح نمایند .
اخبار مرتبط :
مقایسه آنتی ویروسهای KIS و TMIS
کشف نقصهای امنیتی خطرناک در محصولات 2012 کسپرسکی
کسپرسکی اشتباه خود را به طرز بدی اصلاح کرد .
پر فروش ترین شرکتهای آنتی ویروس در سال 2011
دفتر کسپرسکی در ترکیه بسته شد .
چرا کسپرسکی فارسی شد ؟ ( نوآوری یا ناچاری ؟ )
شرکت General Atlantic از خرید سهام کسپرسکی منصرف شد .
بیش از 1 ماه از درج و حذف ناگهانی نسخه های خانگی کسپرسکی می گذرد .
بررسی جامع تروجان پلیس Police Trojan
دیسنا :
پایگاه اطلاع رسانی امنیت فناوری اطلاعات ایران






